The Difference between Admin Connectors or User Connectors
April 15, 2026
Large organizations are rapidly adopting AI-driven assistants and agentic systems to improve productivity. However, this speed of adoption introduces a growing (and often overlooked) risk: user-managed connectors.

User connectors are increasingly becoming part of shadow IT. When left unmanaged, they can lead to severe governance gaps, uncontrolled data replication, and potential data loss.
User Connectors vs. Admin Connectors
In enterprise search the prevailing concept on integrating data in Search has long relied on admin connectors. These are centrally deployed enterprise search connectors and provide controlled access to enterprise systems. Security trimming, as we describe it, e.g. in our blog post here, thus makes sure that search results reflect the content source permissions.
This model ensures:
Centralized governance
Consistent permission enforcement
Auditability and compliance
However, with the rise of SaaS platforms and agentic AI, a lower-level integration approach has entered the market: user connectors.
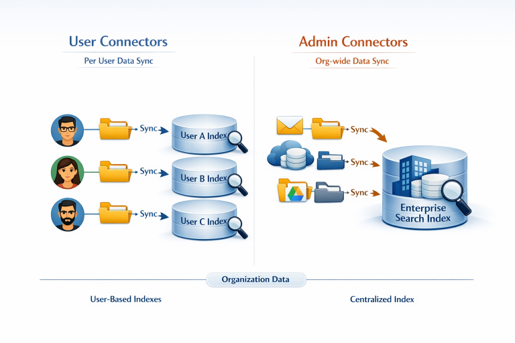
User connectors rely on personal access tokens or delegated permissions. This allows individual users or AI agents acting on their behalf to directly access APIs of business applications. Thus they ingest data into local or cloud-based search engines and AI tools.
From a user perspective, this feels fast and convenient. From an IT governance perspective, it is problematic.
Why are User Connectors so Problematic?
Uncontrolled Computational Overhead
Instead of indexing content once and providing it securely to all users and agents, user connectors index the same data repeatedly. They index all accessible data, once per user.
In an organization with hundreds of knowledge workers, one admin connector would perform a few thousand API calls. For many user connectors, it results in millions of parallel API requests, placing unnecessary load on SaaS platforms and increasing operational risk.
Loss of Permission and Change Propagation Control
When it comes to user connectors, who ensures that permission changes and content updates are reflected across all user-managed indexes?
In the worst case, documents that were restricted or revoked after indexing may remain visible in downstream AI systems. This directly undermines enterprise security models and violates e.g. the principle of least privilege.
Elevated Risk of Data Leakage and Contractual Violations
A particularly critical issue is data exfiltration.
User connectors often ingest data into third-party SaaS or AI platforms. When an organization licenses such platforms as agentic systems, it might not have assessed or approved the large-scale ingestion of sensitive enterprise data into these services.
This creates risks around:
Confidential information leakage
Data residency violations
Contractual and regulatory non-compliance
The Solution
The solution is not to stop AI adoption—but to reclaim control.
Centrally managed admin connectors are the foundation of enterprise AI and RAG architectures. But, IT organizations must move quickly enough to provide approved, centrally governed AI access. Otherwise, user connectors will be used and become a permanent part of shadow IT.
RheinInsights supports organizations in establishing robust AI and IT governance. As a vendor-independent provider, RheinInsights delivers centrally managed admin connectors as part of the RheinInsights Retrieval Suite, enabling secure, scalable, and compliant AI access to enterprise knowledge.